The Penetration Testing with Kali Linux course and the Offensive Security Certified Professional (OSCP) certification was created to not only teach, but also prove someone has the core skills required to do a penetration test. Both the course and the certification exam are hands-on. No multiple choice questions or quizzes at all. To get the OSCP certification you must first go through the Penetration Testing with Kali Linux (PWK) course offered by Offensive Security, then take the exam. Below you will find my experience with going through the course and exam.
Penetration Testing with Kali Linux
Upon starting PWK you are supplied with a lengthy lab guide and videos to teach offensive security techniques that you will use in the lab portion of the course. The lab portion of the course consists of more than 50 machines on a virtual network that consists of 4 subnets. Your goal is to compromise as many machines as you can with the techniques learned from the lab guide.
Penetration Testing process and techniques:
- Information gathering and enumeration
- Discovering security holes and vulnerabilities
- Exploiting vulnerabilities
- Privilege escalation and maintaining access
You will also learn to navigate Kali Linux and the various tools that come bundled with it. The full syllabus for the course can be found here.
I learned more than I could have ever imagined from this course. I am a very hands-on learner; I learn by doing. This course and exam was exactly what I needed.
The point of the lab is pretend to be an attacker by breaking into all the computers. This learning process puts you in a much better position to prevent these things in real life — either at your job or businesses you may be consulting for.
Put yourself in an offensive mindset when approaching a machine. You’ll think about software in new and different ways. As a software developer you aren’t always thinking about how to break things, or what you can do when you break something, or how you can leverage access from one compromised machine to gain access into another. This mindset has helped me become a security conscious developer.
In the lab network, I am proud to say I successfully compromised every machine, in all the subnets. This includes 3 challenge machines, that are meant to be attempted only after you’ve compromised all the other machines.
The names of these are: pain, sufferance, and humble.
You’ll learn why they are named that way. ?These took days to fully compromise. You do not have to compromise every machine to get your certification. The labs are there to prepare for the exam. The better you do in the labs and the more machines you compromise, the higher the chances are in successfully completing the exam.
But that’s not all… reports!
In order to write a good report, take detailed notes. Logging and writing all your findings during the entire process will make the reports MUCH easier to write. The report is what gives the value to the penetration test. Being able to write the report in a way non-technical business executives can understand, but also detailed enough that engineers can fix things, is crucial to a successful report.
Offensive Security Certified Professional Exam
The OSCP exam is where all your hard work is put to the test. Just like the labs, the exam is hands on. It consists of a single network of 5 machines. Each machine has a point value assigned to it, some machines are worth more than others. The total number of points possible is 100, you need at least 70 points to pass. In order to be awarded points for a machine an in depth report with the exact steps it took to compromise the machine is required. This puts further emphasis on the importance of the end report in a penetration test.
The one important detail about the exam is this: you have access to the network for 24 hours.
That’s it.
You have to compromise as many machines within 24 hours to acquire enough points to pass. After your network access expires, you have another 24 hours to write the reports for each machine that was compromised. Good detailed notes end up being crucial at this point since you don’t have access to the network anymore.
I was able to successfully compromise every machine in the exam network. Admittedly, it was not easy… I took roughly 20 hours. However, I did acquire enough points within the first 8 hours to pass, but the final two machines gave me a hard time.
During the end of the exam, I found myself going down a rabbit hole and I was forced to crawl out and refocus. The topics I researched and techniques I learned taught me what I needed to compromise the machine. This experience was all too familiar, having gone down many rabbit holes in the lab.
The next day (or later that day), it was time to write my reports. I kept very detailed notes — took plenty of screenshots, and kept all my working exploit code. It took roughly 5 hours to compile the the lab reports and prepare it for submission.
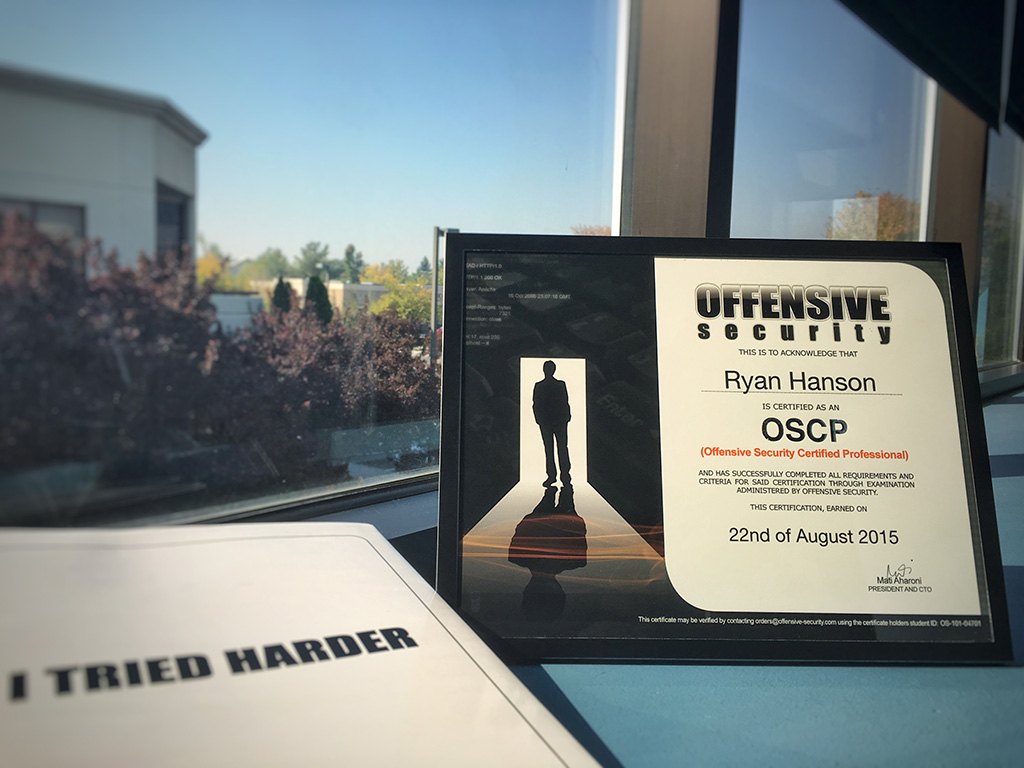
After it was all said and done, the feeling was bittersweet. After spending months in the lab network and hundreds of hours hacking machine after machine, I was sad it was over. It was truly one of the best educational experiences I have ever had.
Feeling accomplished for hacking every machine in both the lab and exam network, you bet I rewarded myself with a ice-cold beer!